Recent News What EDR Platforms Catch: A Quick Breakdown 

What Is the Purpose of an IDS? 

11 Essential Red Team Tools for Cybersecurity Professionals 

What EDR Platforms Catch: A Quick Breakdown 
What Is the Purpose of an IDS? 
11 Essential Red Team Tools for Cybersecurity Professionals 
“There are only two types of companies: those that have been hacked, and those that will be.”
— Robert Mueller, FBI Director, 2012
More News
Microsoft Warns about Russian State-Sponsored Espionage Attacks 
Threat Actors Posing as Ethical Hackers 
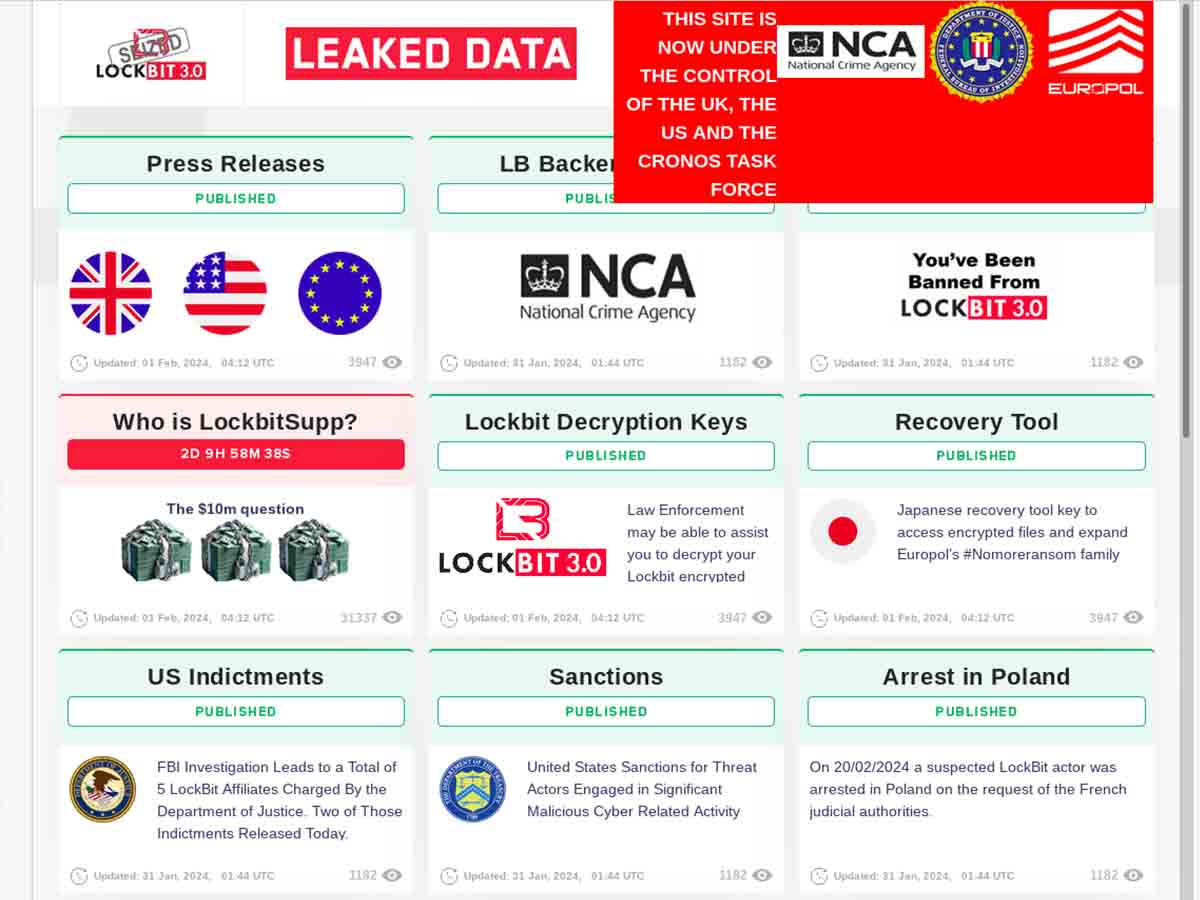
19 Cybercriminals Face Justice in Global Law Enforcement Operation 
Individuals
Richard Stallman: Founder of the Free Software Movement 
Zane Lackey: Co-founder of Signal Sciences 
Wim Remes: Member of the ISC2 Board of Directors 
Whitfield Diffie: Co-inventor of Public Key Cryptography 
Knowledge
VirusTotal: The Cybersecurity Practitioner’s Multi-Engine Shield 
TCP Fingerprinting: How Reliable Is It? 
Trust: How Important Is Trust in Cybersecurity?