Most of us think of viruses and Trojans when we hear the word “malware.”
But in recent years, a different type of malware has taken over as the go-to weapon for cybercriminals: ransomware.
Stay One Step Ahead of Cyber Threats
Increasingly powerful computers and the growing ubiquity of cryptocurrency have fueled this explosion in ransomware attacks. And nobody is immune, be they international corporations, local government, or private citizens.
What Is Ransomware?
Ransomware’s name says it all: it’s a type of malware that locks down your files and devices until you give the attacker a ransom payment.
Attackers use advanced encryption methods to prevent you from using your computer or viewing your files. To restore access and decrypt your files, you’re told to pay a certain amount of money, typically using cryptocurrency to keep the attacker anonymous and untraceable.
How Ransomware Spreads
Ransomware can spread through a variety of vectors, much like other malware.
Some ransomware spreads like worms, scanning networks for devices with vulnerabilities that enable unauthorized access.
Other ransomware relies on social engineering tactics to find new victims, disguising itself as important financial documents or messages from loved ones to trick you into downloading it.
Ransomware also hides inside pirated files, illegal video streams, and cracked software. Illicit websites can also display malicious ads that secretly load the ransomware onto your computer in a drive-by attack.
Other varieties of malware can spread ransomware as part of their destruction. Downloader Trojans, for instance, may be designed to download ransomware, while rootkits can allow attackers to insert ransomware deep into your system where it can’t be detected.
Ransomware Attacks and Encryption
Ransomware generally falls into one of two categories depending on its method of action: screen lockers or encryptors.
Screen Lockers
Screen lockers are considered the less serious variety of ransomware, though they still pose a significant threat, especially to those who aren’t tech-savvy.
Upon starting their computers, victims are presented with a full-screen notice that their device has been locked.
Some notices display government logos, such as the FBI or CIA seal, alongside a terrifying message: you’ve been caught doing something illegal, and law enforcement has locked your computer until you pay a fine. Alternatively, they may impersonate companies like Microsoft, Apple, Google or McAfee, prompting you to pay for an activation key or security patch.
Others do away with the official facade, simply informing you that you’ve been hacked and your computer has been encrypted, and the only way to get it back is to pay up.
But regardless of what they claim, screen lockers don’t actually encrypt your data. Your system is safe, it’s just hidden behind the screen locker — and if you’re able to get rid of the screen locker, you’ll find all of your files intact.
Encryptors
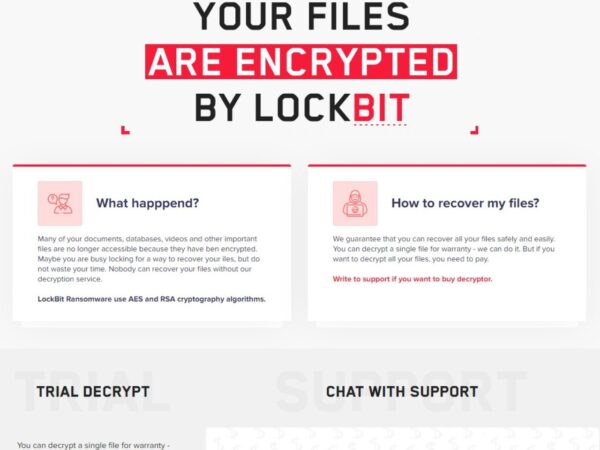
Encryptors are the more dangerous variety of ransomware.
Like screen lockers, they often present you with a full-screen notification that your data has been encrypted. They may also use government logos to look more legitimate, or they may not bother with a disguise at all.
But encryptors aren’t just empty threats. They actually place your files under heavy encryption, often uploading the unencrypted originals to the attacker first.
And unlike with screen lockers, removing the encryptor won’t restore access to your files. Once they’ve been encrypted, only the decryption key can unlock them, and the only person in possession of that key is the attacker.
Though some ransomware uses less secure encryption that can potentially be cracked, savvy attackers use military-grade algorithms. These incredibly advanced ciphers would take even the most powerful supercomputer millions of years to crack.
In those cases, antivirus programs, hard drive recovery tools, and the world’s top cybersecurity experts can’t help you — the only hope is to pay the ransom.
Ransomware Payments and Decryption
Ransomware victims are often forced to act fast. Many attacks place a deadline on the ransom payment, after which the decryption key will be permanently deleted, locking the files forever.
This deadline could be anywhere from a couple of weeks to a few days to just 24 hours.
Screen lockers, of course, don’t actually have a decryption key to erase, so this is an empty threat. But encryptors can and do follow through on their promises.
A few ransomware varieties use weak encryption that’s been cracked, and free decryption programs are available to retrieve the files without paying the ransom. And when these solutions aren’t available, official FBI guidelines advise against giving in to the attacker’s demands.
But with their entire digital lives on the line, many victims decide that they have no choice but to pay up.
Paying the ransom usually involves cryptocurrency, as it allows the attacker to keep their identity and location secret. Victims are instructed to send a certain amount of Bitcoin or other cryptocurrency to the attacker’s crypto address, after which the decryption key will be revealed.
Sometimes, this process works, and the victim is able to retrieve their files.
But all too often, it doesn’t.
Once the attacker has the money, there’s nothing forcing them to actually hand over the key, so many attackers simply take the money and run.
The victim has now lost their money and their files, and with no way to contact the attacker or trace the crypto transaction, that loss is permanent.
Ransomware Attacks, Explained (Video)
Key Ransomware Takeaways
- Ransomware is a type of malware that locks down your files or operating system, demanding a ransom payment to restore functionality.
- Ransomware can spread over networks via system vulnerabilities, hide inside downloaded files or programs, or get loaded onto your computer by other malware.
- Some ransomware simply blocks you from using your computer by locking your screen, while other ransomware actually encrypts your files with a secret key.
- Ransom payments often have a deadline and are usually made in cryptocurrency.
- Paying the ransom doesn’t guarantee that you’ll get your files back — often, the attacker takes the money and disappears without unlocking your system.
History of Ransomware
The first ransomware attack was carried out in 1989 via a floppy disk. Known as the “AIDS Trojan,” its victims were AIDS researchers who ran the disk thinking it contained information about the AIDS virus.
In reality, the disk contained malware that encrypted the victim’s files until a payment of $189 was mailed to a PO Box in Panama. Few people actually paid, and a decryption method was developed the following year, but many victims had already wiped their hard drives to remove the ransomware.
Through the 1990s and early 2000s, ransomware was the subject of many experiments and research, but the public remained largely unaffected by it.
That changed in 2005 when the Cryzip malware was detected in Russia. Cryzip moved the victim’s files into a password-protected zip file, then demanded a $300 ransom to be paid in e-gold, an early digital currency with poor identity verification.
Similar attacks proliferated throughout the 2000s, requiring payment via e-gold, money transfer, or even iTunes gift cards. The debut of Bitcoin in 2008 marked the start of a new era for ransomware, enabling truly anonymous payments for the first time.
As cryptocurrency and advanced encryption made ransomware threats more legitimate and effective, attackers began to switch their focus from individuals to organizations. Companies and governments had more to lose from a ransomware attack — and more money with which to pay ransoms.
Ransomware by the Numbers
- In 2021, 37% of organizations had multiple computers hit by a ransomware attack — and 54% of those attacks succeeded in encrypting the victims’ data
- 32% of organizational ransomware victims paid to get their data back, but on average, only 65% of the data was restored
- As of November 2022, the average ransomware payment was over $258,000
- In 2021, ransomware caused over $20 billion in damages globally, infecting a new device every 11 seconds
Famous Ransomware Attacks
The CryptoLocker Ransomware
First spotted in 2013, CryptoLocker brought ransomware to the public’s attention as one of the most serious cybersecurity threats out there.
Disguising itself as a PDF email attachment from a legitimate company, it locked files behind unbreakable encryption, demanding $400 in Bitcoin for the decryption key. If the ransom wasn’t paid in 72 to 100 hours, the price went up to 10 Bitcoin, then valued at around $2,100.
Within 2 months, the attackers had collected nearly 42,000 Bitcoin — an amount worth over $850 million in July 2022. As many as 41% of victims may have paid up, with many claiming that their files were never decrypted.
The Colonial Pipeline Attack
In May 2021, the hacker group Darkside launched a ransomware attack against the Colonial Pipeline, an oil pipeline responsible for 45% of all fuel used on the East Coast of the US. They demanded a ransom of 75 Bitcoin (~$5 million USD), threatening to release 100 gigabytes of stolen data if they weren’t paid.
The ransom was paid, but the decryption tool sent by the hackers was so slow that all pipeline operations were shut down for six days. Gas stations ran out of fuel, flights were delayed or rerouted, and a national state of emergency was declared.
By the time the pipeline resumed operations, gas prices had spiked to their highest level in 7 years, and over 10,500 gas stations were completely depleted. Eventually, the FBI recovered 63.7 Bitcoins, but the remaining ransom money and the attackers themselves remain at large.
How a Cyber Attack Crippled the Colonial Pipeline (Video)
"Amateurs hack systems, professionals hack people."
-- Bruce Schneier, a renown computer security professional






